| 1 |
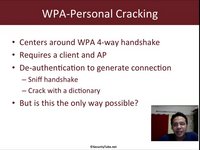 |
Wireless Lan Security Megaprimer Challenge 4: Crack Wpa-Personal With Only Ap |
12 years, 10 months |
Vivek-Ramachandran |
challenge 4, megaprimer, 44con |
20152 |
16 |
| 2 |
 |
Usb Flash Drive Forensics, Philip Polstra - 44con 2011 |
12 years, 3 months |
SecurityTube_Bot |
44con, usb, forensics, philip polstra, 44con-2011 |
5723 |
None |
| 3 |
 |
Trusteer Rapport, Neil Kettle - 44con |
12 years, 2 months |
Securitytube_Poster |
44con, 44con-2011 |
4556 |
None |
| 4 |
 |
Communicating With The Boss, Steve Armstrong - 44con |
12 years, 2 months |
Securitytube_Poster |
44con, 44con-2011 |
4060 |
1 |
| 5 |
 |
Systems Applications Proxy Pwnage, Ian De Villiers - 44con |
12 years, 2 months |
Securitytube_Poster |
44con |
4184 |
None |
| 6 |
 |
Penetration Testing Considered Harmful, Haroon Meer - 44con 2011 |
12 years, 2 months |
SecurityTube_Bot |
44con-2011, 44con |
3462 |
1 |
| 7 |
 |
2012 In Review: Tor And The Censorship Arms Race. Runa A. Sandvik |
10 years, 8 months |
Securitytube_Poster |
securitytube, hacking, hackers, information security, convention, computer security, 44con |
3014 |
None |
| 8 |
 |
Hacking And Forensics On The Go. Phil Polstra |
10 years, 8 months |
Securitytube_Poster |
securitytube, hacking, hackers, information security, convention, computer security, 44con |
3524 |
None |
| 9 |
 |
Software Security Austerity. Ollie Whitehouse |
10 years, 8 months |
Securitytube_Poster |
securitytube, hacking, hackers, information security, convention, computer security, 44con |
2848 |
None |
| 10 |
 |
Surveillance Cameras: The Real-World Has Them Everywhere, Why Not The Computer? |
10 years, 8 months |
Securitytube_Poster |
securitytube, hacking, hackers, information security, convention, computer security, 44con |
3109 |
None |
| 11 |
 |
Modern Post-Exploitation Strategies. |
10 years, 8 months |
Securitytube_Poster |
securitytube, hacking, hackers, information security, convention, computer security, 44con |
3351 |
None |
| 12 |
 |
Cryptanalysis Of The Enigma Machine |
10 years, 8 months |
Securitytube_Poster |
securitytube, hacking, hackers, information security, convention, computer security, 44con |
3556 |
None |
| 13 |
 |
I'M The Butcher, Would You Like Some Beef? Thomas Mackenzie |
10 years, 8 months |
Securitytube_Poster |
securitytube, hacking, hackers, information security, convention, computer security, 44con |
2738 |
None |
| 14 |
 |
Terrorism, Tracking, Privacy And Human Interactions. Daniel Cuthbert And Glenn Wilkinson At 4con 2012 |
10 years, 8 months |
Securitytube_Poster |
securitytube, hacking, hackers, information security, convention, computer security, 44con |
3271 |
None |
| 15 |
 |
Securing The Internet: You're Doing It Wrong (An Infosec Intervention). Jayson Street At 44con 2012 |
10 years, 8 months |
Securitytube_Poster |
securitytube, hacking, hackers, information security, convention, computer security, 44con |
2839 |
None |
| 16 |
 |
An Idiot Abroad. Don A. Bailey At 44con 2012 |
10 years, 8 months |
Securitytube_Poster |
securitytube, hacking, hackers, information security, convention, computer security, 44con |
2745 |
None |
| 17 |
 |
Penetration Testing Considered Harmful, Haroon Meer - 44con |
10 years, 8 months |
Securitytube_Poster |
securitytube, hacking, hackers, information security, convention, computer security, 44con |
2872 |
None |